Safari Security Alert
Sometimes an otherwise secure website may fail to provide a secure way to submit a form, such as a form that contains your password or credit card number. Safari displays a message if you’re about to send information in a nonsecure way, so you can cancel. If you don’t want to see this message, you can turn it off.
To turn off the warning message:
Choose Action menu > Preferences and click Security. (The Action menu is near the upper-right corner of the Safari window, and looks like a gear.)
Deselect “Ask before sending a non-secure form to a secure website.”
What Does Apple Security Alert Mean
If you turn off security warnings, you lose some of your protection against Internet risks. Share personal information and download items only if you are certain that the website you are visiting is trustworthy.
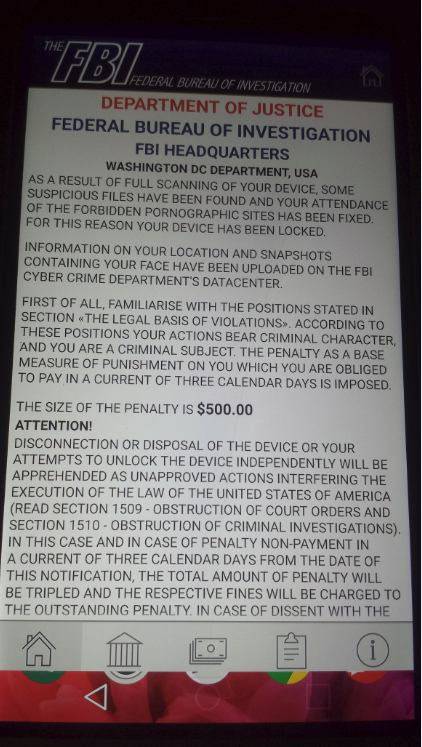
- Apple Security Warning pop-up is whats known as adware. Adware promotes lots of websites to trick you into buying software by displaying fake alerts. It is recommended to always read the Terms.
- Fix: Warning Virus Alert Call Apple – iPhone. If you visited a website using Safari on your iPhone, you may suddenly receive a pop-up message about an Apple Security Breach and to call a toll free number to.
Related Topics
Turning off security warnings
Safari 6.0.5 can be downloaded and installed via Software Update preferences, or from Apple Downloads.
For the protection of our customers, Apple does not disclose, discuss, or confirm security issues until a full investigation has occurred and any necessary patches or releases are available. To learn more about Apple Product Security, see the Apple Product Security website.
For information about the Apple Product Security PGP Key, see 'How to use the Apple Product Security PGP Key.'
Usually, APPLE SECURITY BREACH pop up shows up in the browser when some potentially unwanted program (PUP) gets installed on the device. Typically, redirects to the tech support scam website are triggered by adware. This ad-supported application can modify Chrome’s, Firefox’s, or Safari. Explore the web knowing that strong security protections in Safari help keep you safe. Like iCloud Keychain, which securely stores and autofills your passwords across all your devices. If a password breach is detected, Password Monitoring alerts you.
Where possible, CVE IDs are used to reference the vulnerabilities for further information.
To learn about other Security Updates, see 'Apple Security Updates.'
Safari 6.0.5
Safari Security Updates
WebKit
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5, OS X Mountain Lion v10.8.3
Impact: Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution
Description: Multiple memory corruption issues existed in WebKit. These issues were addressed through improved memory handling.
CVE-ID
CVE-2013-0879 : Atte Kettunen of OUSPG
CVE-2013-0991 : Jay Civelli of the Chromium development community
CVE-2013-0992 : Google Chrome Security Team (Martin Barbella)
CVE-2013-0993 : Google Chrome Security Team (Inferno)
CVE-2013-0994 : David German of Google
CVE-2013-0995 : Google Chrome Security Team (Inferno)
CVE-2013-0996 : Google Chrome Security Team (Inferno)
CVE-2013-0997 : Vitaliy Toropov working with HP's Zero Day Initiative
CVE-2013-0998 : pa_kt working with HP's Zero Day Initiative
CVE-2013-0999 : pa_kt working with HP's Zero Day Initiative
CVE-2013-1000 : Fermin J. Serna of the Google Security Team
CVE-2013-1001 : Ryan Humenick
CVE-2013-1002 : Sergey Glazunov
CVE-2013-1003 : Google Chrome Security Team (Inferno)
CVE-2013-1004 : Google Chrome Security Team (Martin Barbella)
CVE-2013-1005 : Google Chrome Security Team (Martin Barbella)
CVE-2013-1006 : Google Chrome Security Team (Martin Barbella)
CVE-2013-1007 : Google Chrome Security Team (Inferno)
CVE-2013-1008 : Sergey Glazunov
CVE-2013-1009 : Apple
CVE-2013-1010 : miaubiz
CVE-2013-1011 : Google Chrome Security Team (Inferno)
CVE-2013-1023 : Google Chrome Security Team (Inferno)
WebKit
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5, OS X Mountain Lion v10.8.3
Impact: Visiting a maliciously crafted website may lead to a cross-site scripting attack
Description: A cross-site scripting issue existed in the handling of iframes. This issue was addressed through improved origin tracking.
CVE-ID
CVE-2013-1012 : Subodh Iyengar and Erling Ellingsen of Facebook
WebKit
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5, OS X Mountain Lion v10.8.3
Impact: Copying and pasting a malicious HTML snippet may lead to a cross-site scripting attack
Description: A cross-site scripting issue existed in the handling of copied and pasted data in HTML documents. This issue was addressed through additional validation of pasted content.
CVE-ID
CVE-2013-0926 : Aditya Gupta, Subho Halder, and Dev Kar of xys3c (xysec.com)
Safari Security Alert On Iphone
WebKit
Available for: OS X Lion v10.7.5, OS X Lion Server v10.7.5, OS X Mountain Lion v10.8.3
Impact: Following a maliciously crafted link could lead to unexpected behavior on the target site
Description: XSS Auditor may rewrite URLs to prevent cross-site scripting attacks. This may lead to a malicious alteration of the behavior of a form submission. This issue was addressed through improved validation of URLs.
CVE-ID
CVE-2013-1013 : Sam Power of Pentest Limited